Kali Linux – Password Cracking Tool
So to be a good Ethical hacker one must be aware of password cracking techniques. Though it is easy to crack passwords by just using guessing techniques, it is very time consuming and less efficient so in order to automate the task, we have a lot of tools. When it comes to tools Kali Linux is the Operating System that stands first, So here we have a list of tools in Kali Linux that may be used for
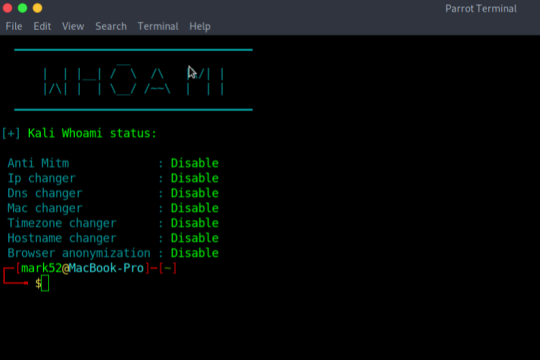
Kali-Whoami – Stay anonymous on Kali Linux
In today’s life, we are surrounded by a lot of cyber security tools and we talk about our online anonymity, but are we really anonymous? A single mistake can reveal our anonymity, so here is a tool that can help us to make anonymity possible and it is called WHOAMI. It is very useful and has a very simple UI. Note: if you are a parrot user then you have to make few changes in the script
8 Useful Firefox Extensions For Ethical Hacking and Security Research
When performing penetration testing of any web-based application, the Mozilla Firefox browser is the most favorable browser for almost every Ethical Hacker and Security Researcher. Mozilla Firefox has proved itself a more featured browser than various browsers like Chrome, Safari, Opera, etc. One of the main reasons behind its popularity is the More Tools features, including Web Developer Tools,
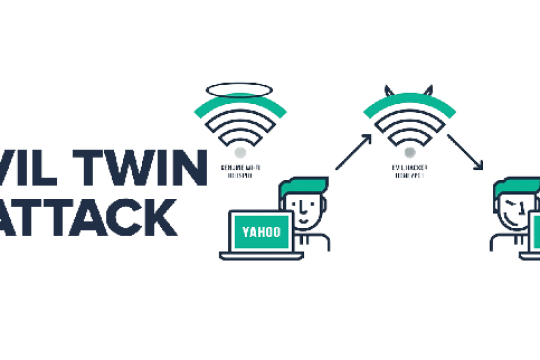
Evil Twin in Kali Linux
Evil Twin Attack is a Wi-Fi hacking technique that tricks the user into connecting to a spoofed targeted network, making it nearly impossible to determine whether the network is real or fake, resulting in the user entering their password in the fake network hosted by the Hacker.
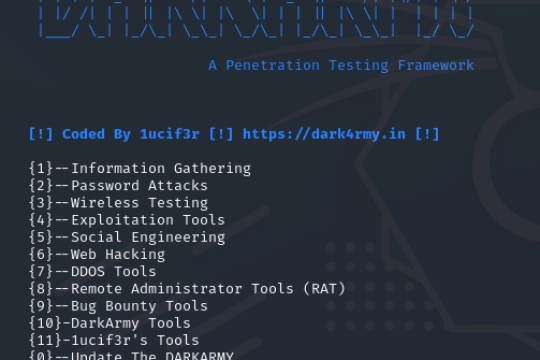
DARKARMY – Penetration Testing Tools
The Darkarmy provides you with a list of tools used for penetration testing all in one place. It saves time for searching for tools under different circumstances. It makes pen testing more straightforward and more user-friendly. It doesn’t have built-in tools, but tools will be installed according to user input. The tool is getting more popular day by day and is used by most beginners in cyber
ShodanX
information gathering tool that harnesses the power of Shodan's extensive database. it offers multiple modes and flexible queries to extract valuable insights for security assessments, reconnaissance, and threat intelligence. With colorful output and intuitive commands, ShodanX empowers users to efficiently gather and analyze data from Shodan's facets, enhancing their cybersecurity efforts.
GoogleDorker - An next level of Google Dorking tool For Cybersecurity
GoogleDorker is a command-line-based Google Dorking tool designed for bug hunters and penetration testers. It enables users to perform in-depth searches using Google Dorks to gather information about their targets. Utilizing Google's provided free APIs, GoogleDorker empowers cybersecurity professionals to conduct comprehensive reconnaissance and vulnerability assessment.
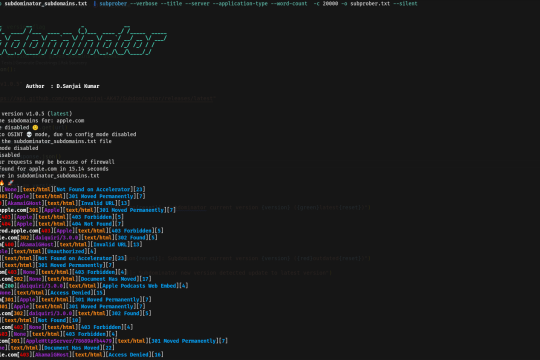
Subdominator - Unleash the Power of Subdomain Enumeration
Subdominator is a powerful tool for passive subdomain enumeration during bug hunting and reconnaissance processes. It is designed to help researchers and cybersecurity professionals discover potential security vulnerabilities by efficiently enumerating subdomains.
Install Honeypot on Linux With Demo
Honeypots are computer applications that collect information from hackers and other criminals. They can be used from a physical or a virtual location, and come in many forms. Honeypots use a wide range of techniques to trap malicious activity and are primarily used in the information security industry
What is Sniffing Attack in System Hacking?
A sniffing attack in system hacking is a form of denial-of-service attack which is carried out by sniffing or capturing packets on the network, and then either sending them repeatedly to a victim machine or replaying them back to the sender with modifications
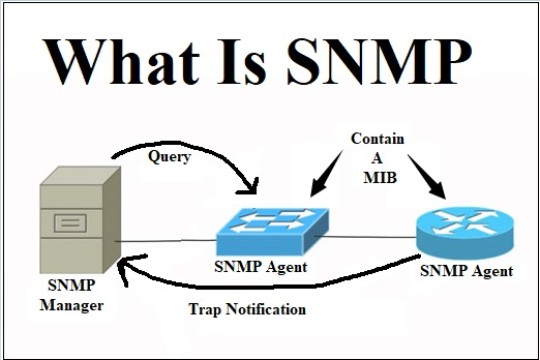
SNMP Enumeration
Simple Network Management Protocol (SNMP) is an application layer protocol that runs on UDP and maintains and manages IP network routers, hubs, and switches. SNMP agents run on networking devices in Windows and UNIX networks.
NetBIOS Enumeration
NetBIOS is an acronym that stands for Network Basic Input Output System. It enables computer communication over a LAN and the sharing of files and printers. TCP/IP network devices are identified using NetBIOS names (Windows)
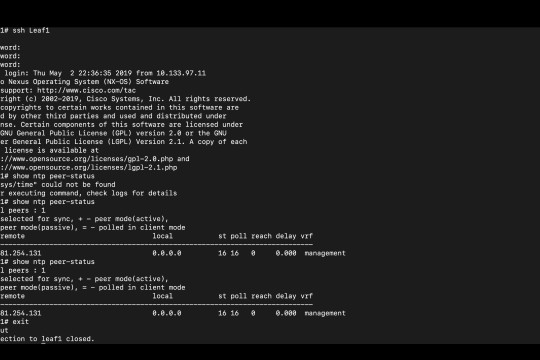
NTP Enumeration
NTP Enumeration is a process by which an attacker can discover NTP servers on the network. This information can then be used to find vulnerable NTP servers, or simply to further enumerate the network
SMTP Enumeration
SMTP (Simple Mail Transfer Protocol) is a set of communication guidelines that allow web applications to perform communication tasks over the internet, including emails. It is a part of the TCP/IP protocol and works on moving emails across the network. SMTP enumeration allows us to identify valid users on the SMTP server. This is done with the built-in SMTP commands using them
Nmap Port Scanning Techniques
Nmap is a security auditing tool used in the security field to actively enumerate a target system/network. It is one of the most extensively used tools by network administrators and conversely attackers for reconnaissance (enumeration), the first step in the 5 phases of hacking
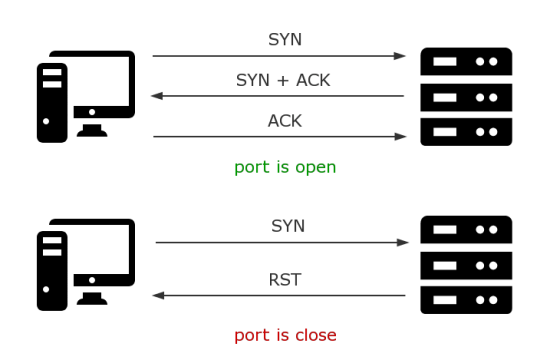
TCP-ACK Scanning?
TCP-ACK is a third step of the TCP 3-Way Handshake process (SYN, SYN-ACK, ACK). In TCP-ACK, the client acknowledges the response of the Server, and establish a connection to proceed with the data transfer and any other communication processes.
WAScan – web application security scanner in Kali Linux
WAScan stands for Web Application Scanner. It is an open-source web application vulnerability scanner. The tool uses the technique of black-box to find various vulnerabilities. This technique will not scan the whole source code of a web application but work like a fuzzer Which means it scans the pages of the whole website or web application. This tool extracts links and forms of the web app
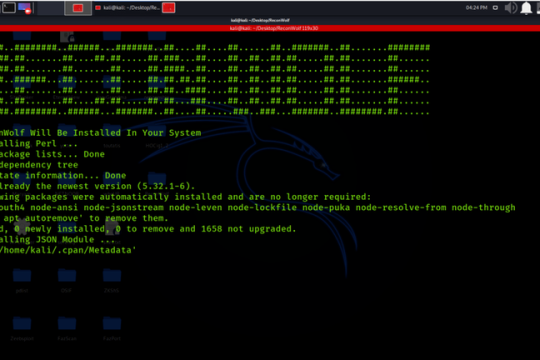
Installation of Reconwolf Tool on Kali Linux OS
Installation of Reconwolf Tool on Kali Linux OS ,Footprinting Through Search Engines