Indian Army to launch command cyber operations and support wings in the face of rising online threats
In a move to augment the operational capabilities along with the absorption of new technologies the Indian Army has decided to create a new wing to handle cyber operations and also plans to create structures to “test bed” the large number and variety of niche tech-enabled equipment being inducted into the Indian Army.
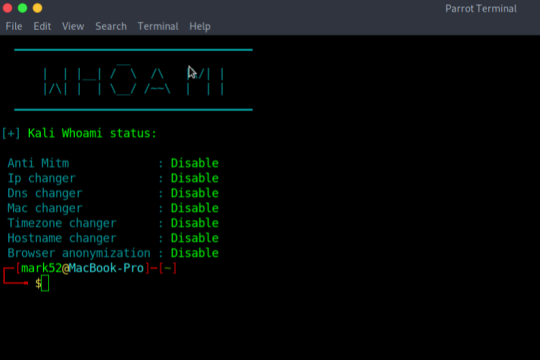
Kali-Whoami – Stay anonymous on Kali Linux
In today’s life, we are surrounded by a lot of cyber security tools and we talk about our online anonymity, but are we really anonymous? A single mistake can reveal our anonymity, so here is a tool that can help us to make anonymity possible and it is called WHOAMI. It is very useful and has a very simple UI. Note: if you are a parrot user then you have to make few changes in the script
8 Useful Firefox Extensions For Ethical Hacking and Security Research
When performing penetration testing of any web-based application, the Mozilla Firefox browser is the most favorable browser for almost every Ethical Hacker and Security Researcher. Mozilla Firefox has proved itself a more featured browser than various browsers like Chrome, Safari, Opera, etc. One of the main reasons behind its popularity is the More Tools features, including Web Developer Tools,
7 Ways To Earn Money as an Ethical Hacker
Ethical hacking, also known as “white hat” hacking, is the practice of using computer security skills for the purpose of testing and improving the security of a computer system or network. This type of hacking is conducted with the permission of the owner of the system or network, and the aim is to identify vulnerabilities and weaknesses that could be exploited by malicious hackers.
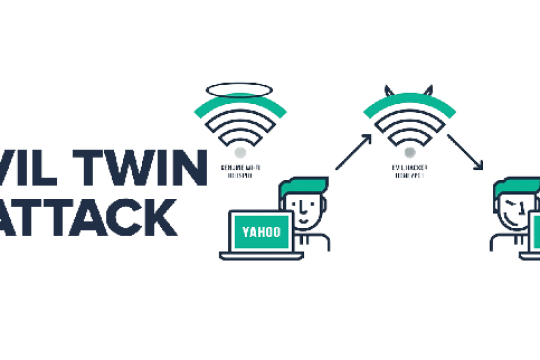
Evil Twin in Kali Linux
Evil Twin Attack is a Wi-Fi hacking technique that tricks the user into connecting to a spoofed targeted network, making it nearly impossible to determine whether the network is real or fake, resulting in the user entering their password in the fake network hosted by the Hacker.
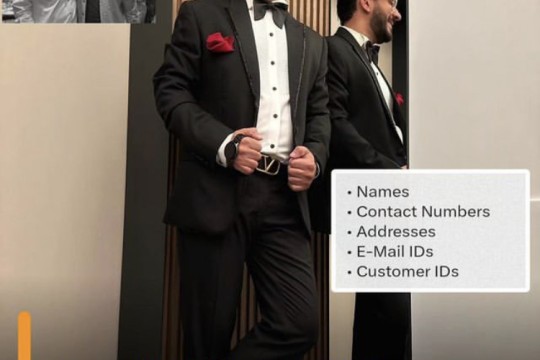
Personal data of 7.5 million Boat customers data leaked on dark web
Boat, one of India's leading wearables brands in India, has reportedly suffered a massive data breach. According to a report by Forbes India, personal data of more than 7.5 million customers has been leaked on the dark web. The report cites a hacker named ShopifyGUY, who claims to have leaked the data on dark web.
Skills Required to Become a Ethical Hacker
Ethical Hacking is compromising computer systems for assessing security and acting in good faith by informing the vulnerable party. Ethical hacking is a key skill for many job roles related to securing the online assets of an organization.
Why Hackers Use Kali Linux?
New technologies are rapidly allowing us to transfer crucial data over the internet. Therefore, hacking has become so much more popular and common nowadays. Ethical hackers do white hat hacking to find and repair the vulnerabilities of the system, which increase the security of the systems. On the other side, black hat hacking is used for breaching the system and accessing the system with no pre
Install Honeypot on Linux With Demo
Honeypots are computer applications that collect information from hackers and other criminals. They can be used from a physical or a virtual location, and come in many forms. Honeypots use a wide range of techniques to trap malicious activity and are primarily used in the information security industry
Ivanti Vulnerability Exploited to Install 'DSLog' Backdoor on 670+ IT Infrastructures
Threat actors are leveraging a recently disclosed security flaw impacting Ivanti Connect Secure, Policy Secure, and ZTA gateways to deploy a backdoor codenamed DSLog on susceptible devices.
What is Sniffing Attack in System Hacking?
A sniffing attack in system hacking is a form of denial-of-service attack which is carried out by sniffing or capturing packets on the network, and then either sending them repeatedly to a victim machine or replaying them back to the sender with modifications
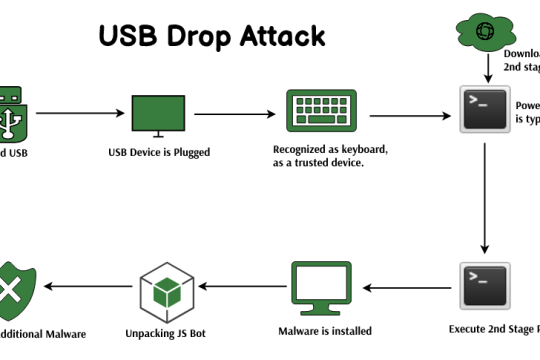
USB Drop Attack in System Hacking
The USB drop attack is a client-side attack in system hacking. This means that an attacker must be physically near the victim and plug a malicious USB device into the victim’s computer to launch this type of attack. This type of cybersecurity hack is often used by cybercriminals to steal data or install malware onto a vulnerable PC
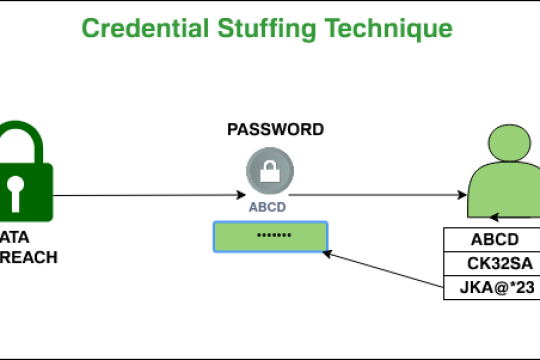
Brute Force Attack
A Brute force attack is a well known breaking technique, by certain records, brute force attacks represented five percent of affirmed security ruptures. A brute force attack includes ‘speculating’ username and passwords to increase unapproved access to a framework. Brute force is a straightforward attack strategy and has a high achievement rate.
Windows Hacking
Windows OS is a graphical user interface (GUI) operating system developed by Microsoft. It was first released in 1985 as an add-on for MS-DOS, which was the most popular version of MS-DOS at that time. In its early days, Windows OS was known as “Microsoft DOS” or “MS-DOS” and later on it became known as Windows 1.0 in 1987. The name changed to Windows NT when it was released in 1993 and then again
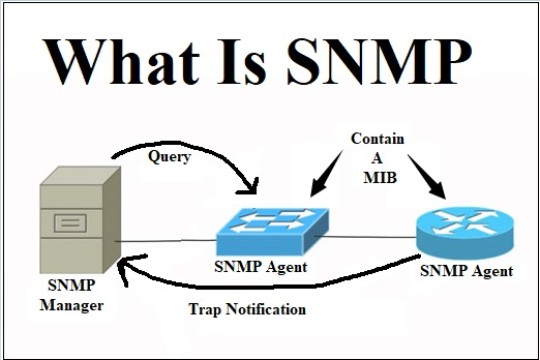
SNMP Enumeration
Simple Network Management Protocol (SNMP) is an application layer protocol that runs on UDP and maintains and manages IP network routers, hubs, and switches. SNMP agents run on networking devices in Windows and UNIX networks.
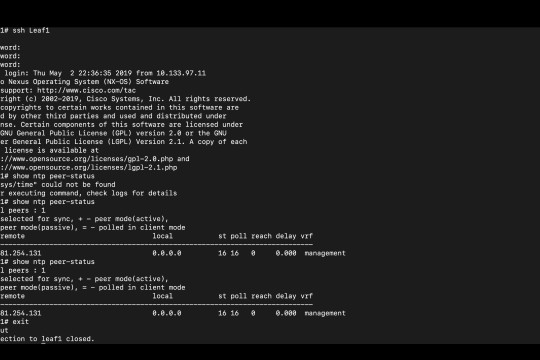
NTP Enumeration
NTP Enumeration is a process by which an attacker can discover NTP servers on the network. This information can then be used to find vulnerable NTP servers, or simply to further enumerate the network
Cyber Security – Types of Enumeration
Enumeration is fundamentally checking. An attacker sets up a functioning associated with the objective host. The weaknesses are then tallied and evaluated. It is done mostly to look for assaults and dangers to the objective framework. Enumeration is utilized to gather usernames, hostname, IP addresses, passwords, arrangements, and so on
WAScan – web application security scanner in Kali Linux
WAScan stands for Web Application Scanner. It is an open-source web application vulnerability scanner. The tool uses the technique of black-box to find various vulnerabilities. This technique will not scan the whole source code of a web application but work like a fuzzer Which means it scans the pages of the whole website or web application. This tool extracts links and forms of the web app