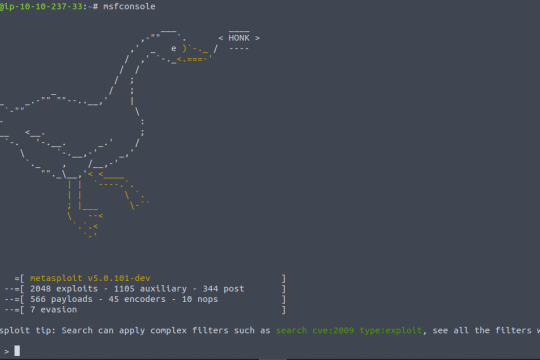
Persistent Reverse Shell with Metasploit in Kali Linux
A reverse shell is a type of network connection in which a command shell is executed on a remote machine, and the input and output of the shell are transmitted over the network back to the local machine. This allows a user on the local machine to execute commands on the remote machine and receive the output of those commands.
GoogleDorker - An next level of Google Dorking tool For Cybersecurity
GoogleDorker is a command-line-based Google Dorking tool designed for bug hunters and penetration testers. It enables users to perform in-depth searches using Google Dorks to gather information about their targets. Utilizing Google's provided free APIs, GoogleDorker empowers cybersecurity professionals to conduct comprehensive reconnaissance and vulnerability assessment.
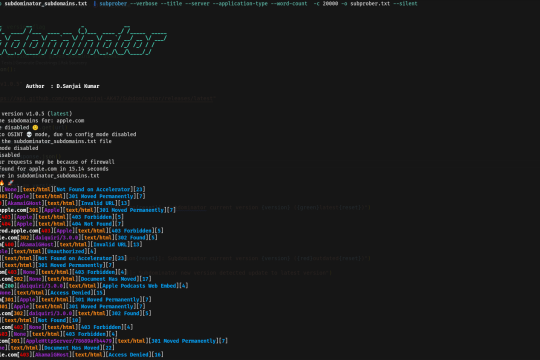
Subdominator - Unleash the Power of Subdomain Enumeration
Subdominator is a powerful tool for passive subdomain enumeration during bug hunting and reconnaissance processes. It is designed to help researchers and cybersecurity professionals discover potential security vulnerabilities by efficiently enumerating subdomains.
Install Honeypot on Linux With Demo
Honeypots are computer applications that collect information from hackers and other criminals. They can be used from a physical or a virtual location, and come in many forms. Honeypots use a wide range of techniques to trap malicious activity and are primarily used in the information security industry