Kali Linux – Password Cracking Tool
So to be a good Ethical hacker one must be aware of password cracking techniques. Though it is easy to crack passwords by just using guessing techniques, it is very time consuming and less efficient so in order to automate the task, we have a lot of tools. When it comes to tools Kali Linux is the Operating System that stands first, So here we have a list of tools in Kali Linux that may be used for
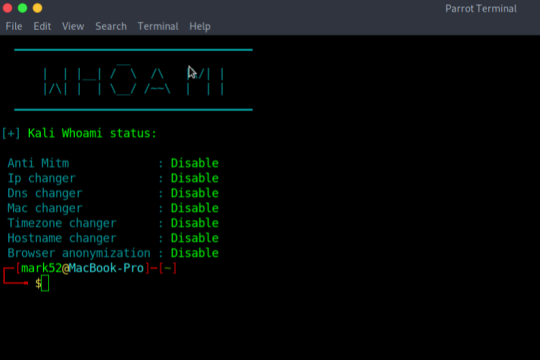
Kali-Whoami – Stay anonymous on Kali Linux
In today’s life, we are surrounded by a lot of cyber security tools and we talk about our online anonymity, but are we really anonymous? A single mistake can reveal our anonymity, so here is a tool that can help us to make anonymity possible and it is called WHOAMI. It is very useful and has a very simple UI. Note: if you are a parrot user then you have to make few changes in the script
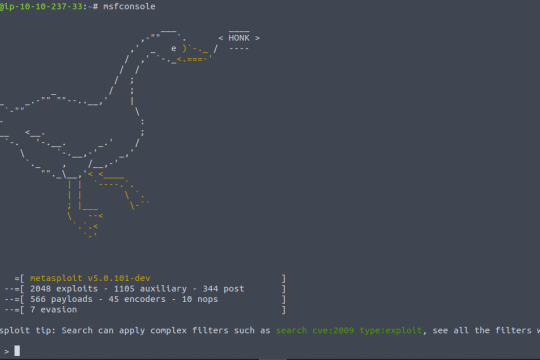
Persistent Reverse Shell with Metasploit in Kali Linux
A reverse shell is a type of network connection in which a command shell is executed on a remote machine, and the input and output of the shell are transmitted over the network back to the local machine. This allows a user on the local machine to execute commands on the remote machine and receive the output of those commands.
ShodanX
information gathering tool that harnesses the power of Shodan's extensive database. it offers multiple modes and flexible queries to extract valuable insights for security assessments, reconnaissance, and threat intelligence. With colorful output and intuitive commands, ShodanX empowers users to efficiently gather and analyze data from Shodan's facets, enhancing their cybersecurity efforts.
What is Sniffing Attack in System Hacking?
A sniffing attack in system hacking is a form of denial-of-service attack which is carried out by sniffing or capturing packets on the network, and then either sending them repeatedly to a victim machine or replaying them back to the sender with modifications
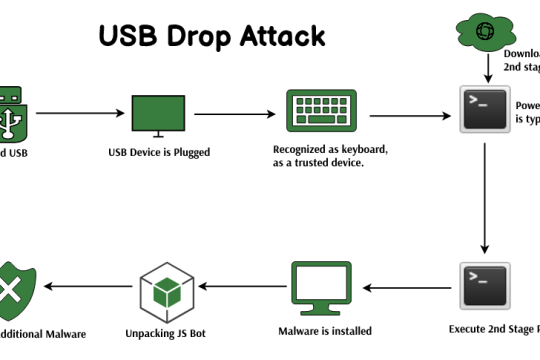
USB Drop Attack in System Hacking
The USB drop attack is a client-side attack in system hacking. This means that an attacker must be physically near the victim and plug a malicious USB device into the victim’s computer to launch this type of attack. This type of cybersecurity hack is often used by cybercriminals to steal data or install malware onto a vulnerable PC
WAScan – web application security scanner in Kali Linux
WAScan stands for Web Application Scanner. It is an open-source web application vulnerability scanner. The tool uses the technique of black-box to find various vulnerabilities. This technique will not scan the whole source code of a web application but work like a fuzzer Which means it scans the pages of the whole website or web application. This tool extracts links and forms of the web app
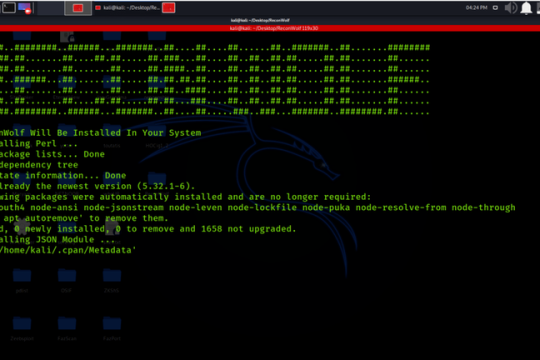
Installation of Reconwolf Tool on Kali Linux OS
Installation of Reconwolf Tool on Kali Linux OS ,Footprinting Through Search Engines