Hackers os
Ethical hacking is identifying weaknesses in computer systems or networks to exploit its vulnerabilities so they can be fixed later.Hackers use various techniques to identify threats and thereby increase the security of the device. These people can utilize Linux based operating system to hack PC or network
Durex India customers may have leaked online
Durex India, a well-known brand for condoms and personal lubricants, has accidentally exposed sensitive information of its customers through its official website. TechCrunch was the first one to report about this breach, which has raised serious concerns about privacy and security, especially considering the intimate nature of the products involved.
Multi-Stage ValleyRAT Targets Chinese Users with Advanced Tactics
Chinese-speaking users are the target of an ongoing campaign that distributes a malware known as ValleyRAT."ValleyRAT is a multi-stage malware that utilizes diverse techniques to monitor and control its victims and deploy arbitrary plugins to cause further damage," Fortinet FortiGuard Labs researchers Eduardo Altares and Joie Salvio said.
Indian Army to launch command cyber operations and support wings in the face of rising online threats
In a move to augment the operational capabilities along with the absorption of new technologies the Indian Army has decided to create a new wing to handle cyber operations and also plans to create structures to “test bed” the large number and variety of niche tech-enabled equipment being inducted into the Indian Army.
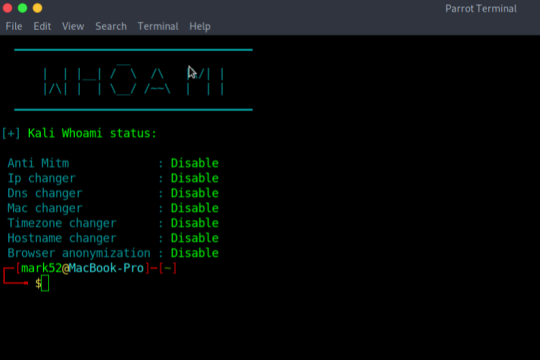
Kali-Whoami – Stay anonymous on Kali Linux
In today’s life, we are surrounded by a lot of cyber security tools and we talk about our online anonymity, but are we really anonymous? A single mistake can reveal our anonymity, so here is a tool that can help us to make anonymity possible and it is called WHOAMI. It is very useful and has a very simple UI. Note: if you are a parrot user then you have to make few changes in the script
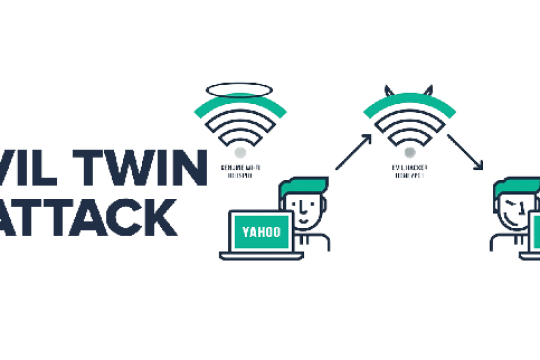
Evil Twin in Kali Linux
Evil Twin Attack is a Wi-Fi hacking technique that tricks the user into connecting to a spoofed targeted network, making it nearly impossible to determine whether the network is real or fake, resulting in the user entering their password in the fake network hosted by the Hacker.
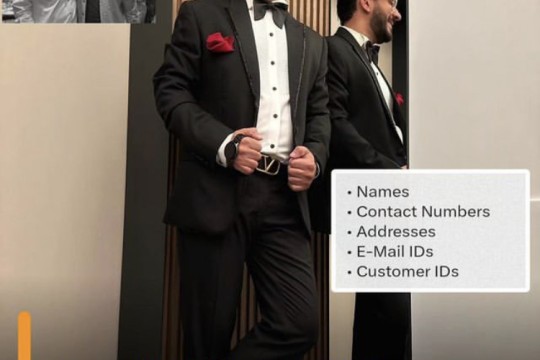
Personal data of 7.5 million Boat customers data leaked on dark web
Boat, one of India's leading wearables brands in India, has reportedly suffered a massive data breach. According to a report by Forbes India, personal data of more than 7.5 million customers has been leaked on the dark web. The report cites a hacker named ShopifyGUY, who claims to have leaked the data on dark web.
ShodanX
information gathering tool that harnesses the power of Shodan's extensive database. it offers multiple modes and flexible queries to extract valuable insights for security assessments, reconnaissance, and threat intelligence. With colorful output and intuitive commands, ShodanX empowers users to efficiently gather and analyze data from Shodan's facets, enhancing their cybersecurity efforts.
GoogleDorker - An next level of Google Dorking tool For Cybersecurity
GoogleDorker is a command-line-based Google Dorking tool designed for bug hunters and penetration testers. It enables users to perform in-depth searches using Google Dorks to gather information about their targets. Utilizing Google's provided free APIs, GoogleDorker empowers cybersecurity professionals to conduct comprehensive reconnaissance and vulnerability assessment.
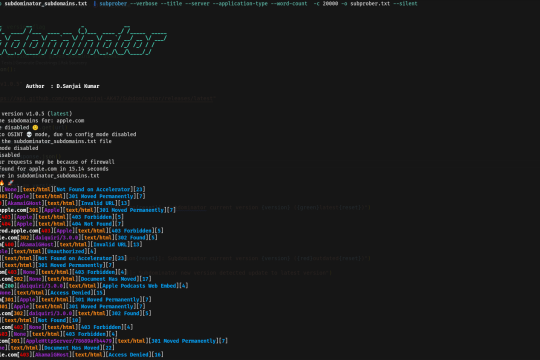
Subdominator - Unleash the Power of Subdomain Enumeration
Subdominator is a powerful tool for passive subdomain enumeration during bug hunting and reconnaissance processes. It is designed to help researchers and cybersecurity professionals discover potential security vulnerabilities by efficiently enumerating subdomains.
Ivanti Vulnerability Exploited to Install 'DSLog' Backdoor on 670+ IT Infrastructures
Threat actors are leveraging a recently disclosed security flaw impacting Ivanti Connect Secure, Policy Secure, and ZTA gateways to deploy a backdoor codenamed DSLog on susceptible devices.
What is Sniffing Attack in System Hacking?
A sniffing attack in system hacking is a form of denial-of-service attack which is carried out by sniffing or capturing packets on the network, and then either sending them repeatedly to a victim machine or replaying them back to the sender with modifications
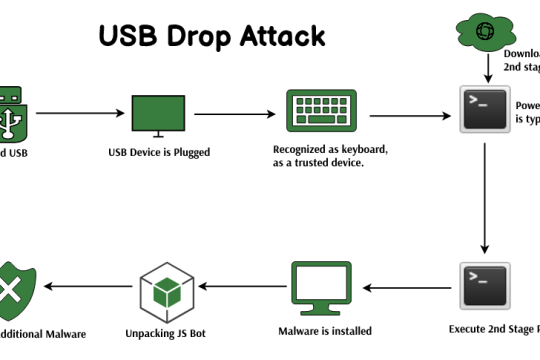
USB Drop Attack in System Hacking
The USB drop attack is a client-side attack in system hacking. This means that an attacker must be physically near the victim and plug a malicious USB device into the victim’s computer to launch this type of attack. This type of cybersecurity hack is often used by cybercriminals to steal data or install malware onto a vulnerable PC
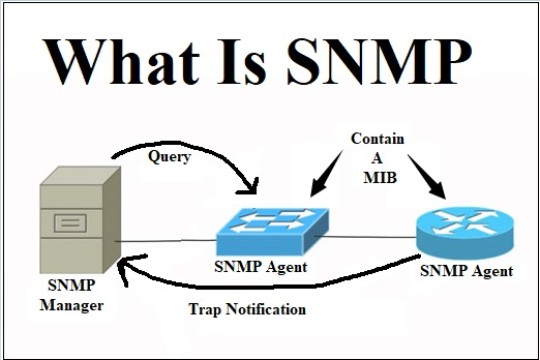
SNMP Enumeration
Simple Network Management Protocol (SNMP) is an application layer protocol that runs on UDP and maintains and manages IP network routers, hubs, and switches. SNMP agents run on networking devices in Windows and UNIX networks.
NetBIOS Enumeration
NetBIOS is an acronym that stands for Network Basic Input Output System. It enables computer communication over a LAN and the sharing of files and printers. TCP/IP network devices are identified using NetBIOS names (Windows)
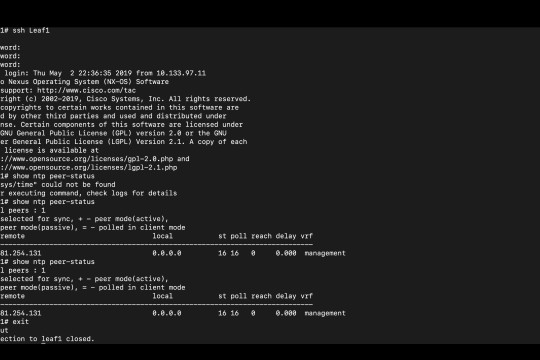
NTP Enumeration
NTP Enumeration is a process by which an attacker can discover NTP servers on the network. This information can then be used to find vulnerable NTP servers, or simply to further enumerate the network
SMTP Enumeration
SMTP (Simple Mail Transfer Protocol) is a set of communication guidelines that allow web applications to perform communication tasks over the internet, including emails. It is a part of the TCP/IP protocol and works on moving emails across the network. SMTP enumeration allows us to identify valid users on the SMTP server. This is done with the built-in SMTP commands using them
Cyber Security – Types of Enumeration
Enumeration is fundamentally checking. An attacker sets up a functioning associated with the objective host. The weaknesses are then tallied and evaluated. It is done mostly to look for assaults and dangers to the objective framework. Enumeration is utilized to gather usernames, hostname, IP addresses, passwords, arrangements, and so on
Nmap Port Scanning Techniques
Nmap is a security auditing tool used in the security field to actively enumerate a target system/network. It is one of the most extensively used tools by network administrators and conversely attackers for reconnaissance (enumeration), the first step in the 5 phases of hacking