Install Honeypot on Linux With Demo
Honeypots are computer applications that collect information from hackers and other criminals. They can be used from a physical or a virtual location, and come in many forms. Honeypots use a wide range of techniques to trap malicious activity and are primarily used in the information security industry
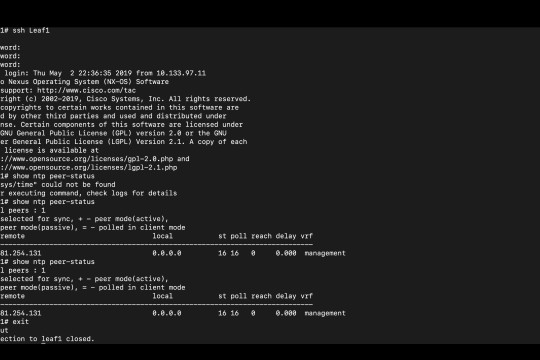
NTP Enumeration
NTP Enumeration is a process by which an attacker can discover NTP servers on the network. This information can then be used to find vulnerable NTP servers, or simply to further enumerate the network
Credentialed Vulnerability Scan?
Cyber Security prevention is the need of today’s generation. Awareness and knowledge of proper security techniques must be spread among the cyber-using generation to prevent frequent cyber attacks from taking place in the cyber world. Here, in this article, we will discuss one very important scanning technique – Credentialed Vulnerability Scan that has played a vital role in preventing cyber