Russian Hacker Jailed 3+ Years for Selling Stolen Credentials on Dark Web
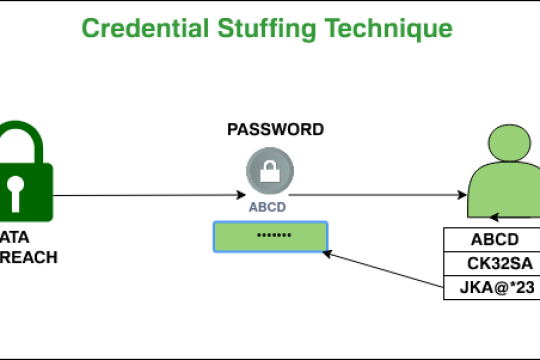
A 27-year-old Russian national has been sentenced to over three years in prison in the U.S. for peddling financial information, login credentials, and other personally identifying information (PII) on a now-defunct dark web marketplace called Slilpp.
Indian Army to launch command cyber operations and support wings in the face of rising online threats
In a move to augment the operational capabilities along with the absorption of new technologies the Indian Army has decided to create a new wing to handle cyber operations and also plans to create structures to “test bed” the large number and variety of niche tech-enabled equipment being inducted into the Indian Army.
Why Hackers Use Kali Linux?
New technologies are rapidly allowing us to transfer crucial data over the internet. Therefore, hacking has become so much more popular and common nowadays. Ethical hackers do white hat hacking to find and repair the vulnerabilities of the system, which increase the security of the systems. On the other side, black hat hacking is used for breaching the system and accessing the system with no pre
Install Honeypot on Linux With Demo
Honeypots are computer applications that collect information from hackers and other criminals. They can be used from a physical or a virtual location, and come in many forms. Honeypots use a wide range of techniques to trap malicious activity and are primarily used in the information security industry
Windows Hacking
Windows OS is a graphical user interface (GUI) operating system developed by Microsoft. It was first released in 1985 as an add-on for MS-DOS, which was the most popular version of MS-DOS at that time. In its early days, Windows OS was known as “Microsoft DOS” or “MS-DOS” and later on it became known as Windows 1.0 in 1987. The name changed to Windows NT when it was released in 1993 and then again
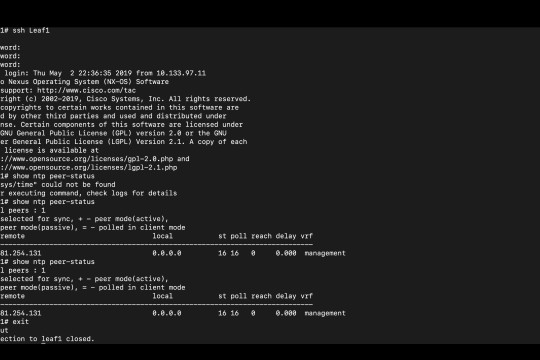
NTP Enumeration
NTP Enumeration is a process by which an attacker can discover NTP servers on the network. This information can then be used to find vulnerable NTP servers, or simply to further enumerate the network